What Is a Security Incident Report?
A security incident report is a formal document that records any event compromising or threatening the physical security of a facility, its occupants, or its assets. Unlike workplace incident reports (which focus on employee safety and OSHA compliance) or police reports (which are generated by law enforcement), a security incident report is created by the organization's security team — contract guards, in-house security officers, facility managers, or loss prevention specialists — to document breaches of physical security controls and initiate the organization's response. The report captures what happened, what security measures failed or were circumvented, what evidence is available, and what corrective actions are needed to prevent recurrence.
Physical security incidents span a wide range of severity: from a tailgating violation at a controlled access point (low severity, high frequency) to an armed intrusion or bomb threat (high severity, low frequency). The common thread is that each event represents a failure or gap in the organization's security posture — a door left propped open, a camera with a blind spot, a guard post left unattended, a badge that should have been deactivated, or an alarm that was not monitored. Every incident, regardless of severity, provides intelligence about vulnerabilities that can be exploited by increasingly sophisticated threats. Organizations that document and analyze security incidents systematically develop a far more accurate understanding of their risk landscape than those that rely on periodic security assessments alone.
The security incident report also serves critical legal and insurance functions. In premises liability litigation (a visitor injured during a security breach, an employee assaulted in a parking garage), the report establishes what the organization knew about the threat and what protective measures were in place. For insurance claims following theft, vandalism, or property damage, the report provides the documented factual basis the carrier requires. And for regulatory compliance in industries with physical security mandates (chemical facilities under CFATS, nuclear facilities under NRC regulations, defense contractors under NISPOM), the report demonstrates that security events are being tracked, investigated, and corrected as required.
Surveillance Evidence
Document and preserve video evidence with proper chain of custody protocols
Access Control Analysis
Correlate badge swipes, denied entries, and anomalies with incident timelines
Loss Prevention
Build intelligence on theft patterns, shrinkage trends, and vulnerability exposure
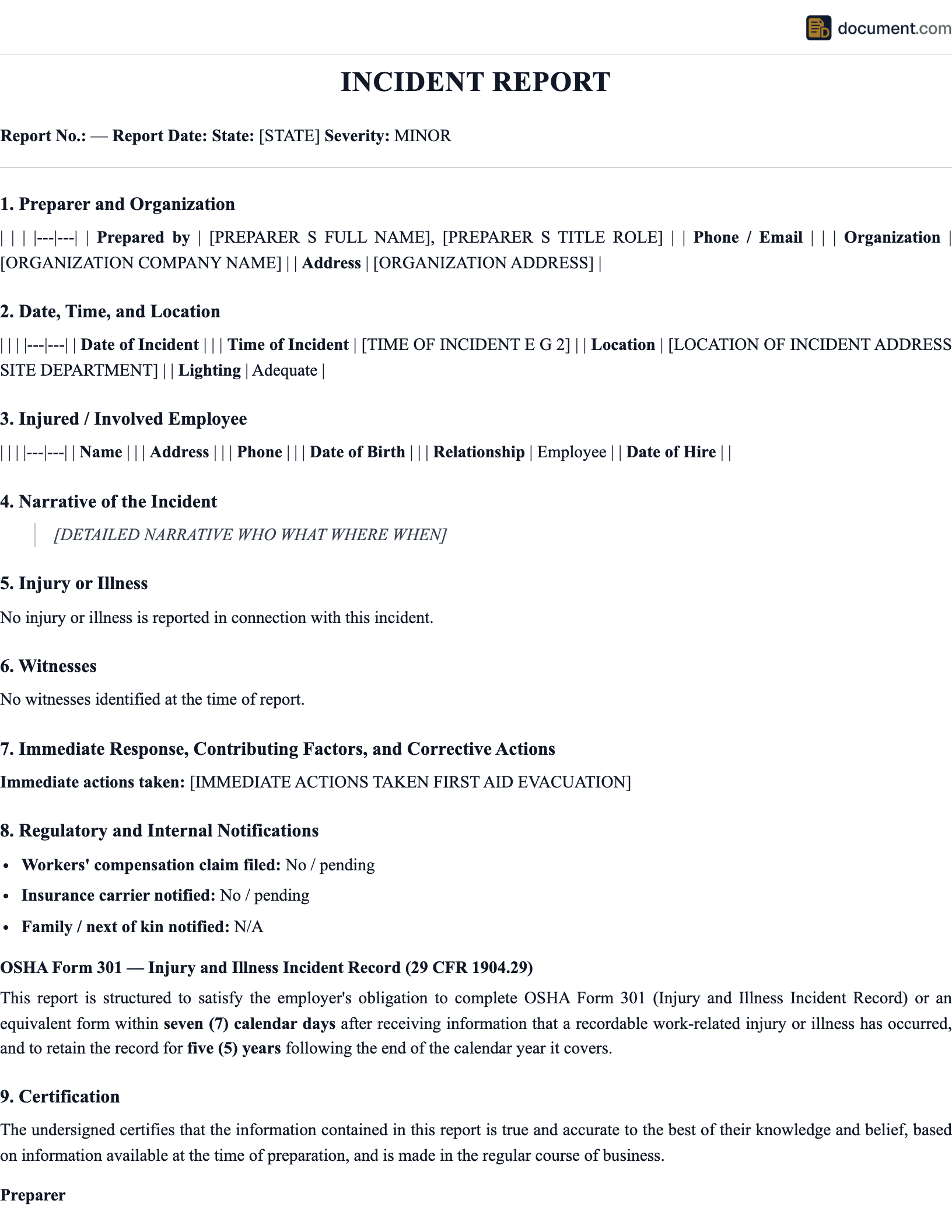
Security Incident Report Form Preview
Below is a condensed preview showing how the key sections of a security incident report are structured. Your final document will be customized for your facility type, security program requirements, and the specific nature of the incident.
SECURITY INCIDENT REPORT
Report #[Number]
1. INCIDENT DETAILS
Date: [Date] Time: [Time] Location: [Building / Zone / Post]
2. INCIDENT TYPE
Category: [Unauthorized Access / Theft / Trespass / Vandalism / Threat / Other]
3. INVOLVED PERSONS
Subject: [Name or Description] Status: [Employee / Visitor / Unknown / Trespasser]
4. OFFICER NARRATIVE
[Chronological account of discovery, response, and actions taken]
5. EVIDENCE & SURVEILLANCE
Cameras: [Camera IDs / Time Range] Access logs: [Reader / Entries] Physical evidence: [Description / Location]
6. NOTIFICATIONS & DISPOSITION
Law enforcement: [Agency / Case #] Management: [Name / Time] Status: [Open / Closed / Referred]
Key Components of a Security Incident Report
A thorough security incident report documents not only what happened, but what security controls were in place, which controls failed, what evidence is available, and what corrective actions will close the vulnerability. These are the essential elements.
Incident Classification & Severity
Categorize the event by type (unauthorized access, theft, trespass, vandalism, assault, suspicious activity, alarm activation, access control failure) and severity level. Severity should account for both actual impact (property loss, injury, data exposure) and potential impact (what could have happened if the breach had not been detected). This classification drives investigation priority, management notification requirements, and corrective action urgency.
Security Officer Narrative
A detailed, chronological, first-person account by the security officer or first responder: how the incident was discovered or reported, what the officer observed upon arrival, what actions were taken (area secured, suspect contacted, evidence preserved, alarm responded to), and the outcome. The narrative should use specific times, locations, and descriptions — "at 0237 hours, I observed the east loading dock roll-up door in the full open position" rather than "I found a door open."
Surveillance & Electronic Evidence
Documentation of all electronic evidence reviewed or preserved: surveillance camera footage (camera numbers, time ranges, export details), access control logs (badge swipes, denied entries, door-held-open alarms), alarm system activations (zone, time, response), and any other electronic systems (intercom recordings, vehicle license plate readers, visitor management system entries). Each evidence item must have its chain of custody initiated in the report.
Property & Loss Documentation
A detailed inventory of any property stolen, damaged, or compromised: item descriptions, serial numbers, asset tag numbers, estimated values, and photographs. For theft incidents, document what security measures were in place (locks, cables, cages, alarms) and how they were defeated. This documentation is essential for insurance claims, law enforcement reports, and loss prevention analysis.
Security Control Assessment
An analysis of which security controls were in place at the time of the incident and which failed, were circumvented, or were absent. This section identifies the specific vulnerability that was exploited: a camera blind spot, a door with a broken lock, a deactivated badge that should have been collected, a guard post left unattended, or a perimeter fence with a gap. This assessment is the most important section for preventing future incidents.
Corrective Actions & Recommendations
Specific, actionable measures to close the identified vulnerability: repair or replace physical security hardware, adjust camera angles or coverage, modify access control permissions, update patrol routes, add lighting, revise procedures, or increase staffing. Each action should have an assigned owner, a completion deadline, and a method for verifying effectiveness. Recommendations should be prioritized by risk reduction potential.
How to Write a Security Incident Report
Security incident reports must be accurate, detailed, and timely. They are often the first document reviewed by management, law enforcement, insurance adjusters, and attorneys. Follow these steps to produce a report that stands up to scrutiny.
Secure the scene and ensure safety
Prioritize the safety of all individuals in the area. If the incident involves an active threat, follow the facility's emergency response plan. Secure the perimeter to preserve evidence and prevent additional unauthorized access. If the situation requires law enforcement or emergency medical services, contact them immediately before beginning documentation.
Preserve all electronic evidence immediately
Flag surveillance footage covering the incident area and timeframe for preservation — many systems overwrite on a 30-90 day cycle. Export relevant access control logs. Save alarm activation records. If the incident involves digital systems, preserve system logs and audit trails. Document the exact cameras, readers, and time ranges preserved. This step is time-critical and should happen before the detailed report is written.
Document the scene with photographs and notes
Photograph the incident location from multiple angles, including wide shots for context and close-ups of specific evidence (damaged locks, forced entry marks, broken windows, items out of place). Take notes on environmental conditions — lighting, weather, visibility, noise. Mark the exact location of physical evidence before it is collected or moved.
Collect witness statements
Interview witnesses and involved parties separately. Record their account of what they saw, heard, and did. Note the witness's location at the time of the event, their relationship to the facility (employee, visitor, contractor), and any factors affecting their observation. Obtain written statements where possible and document the interview time and setting.
Write the report narrative and complete all sections
Write a chronological, factual narrative covering discovery, response, investigation, and outcome. Complete all form sections: classification, severity, involved persons, evidence inventory, property loss, notifications, and preliminary corrective actions. Use specific times, locations, and descriptions. Avoid opinions, conclusions about intent, and speculative language. File the report within the timeframe required by your organization's security operations manual.
Notify management and coordinate with law enforcement
Follow the escalation matrix to notify appropriate management levels based on incident severity. If the incident was reported to law enforcement, document the agency, responding officer, and case number. Coordinate evidence sharing with investigators. Submit the report to the security operations center, risk management, and any other stakeholders designated in your organization's incident response plan.
Frequently Asked Questions
Common questions about security incident reporting, surveillance documentation, access control analysis, loss prevention, law enforcement coordination, and evidence preservation.
Official Resources
Professional organizations, federal agencies, and industry resources for physical security incident management, loss prevention, and facility protection.
ASIS International
Global security professional organization with standards, certifications (CPP, PSP, PCI), and best practices
CISA - Physical Security
Federal guidance on facility security assessments, threat mitigation, and infrastructure protection
DHS - CFATS Chemical Facility Standards
Anti-terrorism security standards for high-risk chemical facilities
NRF - National Retail Security Survey
Annual industry benchmarks for retail shrinkage, theft, and loss prevention
IFPO - International Foundation for Protection Officers
Training resources, certifications, and report writing standards for security officers
SIA - Security Industry Association
Trade association for electronic and physical security technology providers
Create your Security Incident Report in under 10 minutes.
Answer a few questions and download a compliant, attorney-drafted document ready for your state.